Strategic Thinking for Cyber Resilience: The Six Thinking Hats in VAPT
Cybersecurity is no longer the exclusive domain of IT departments; it is now a strategic business imperative for every boardroom. For C-Suite executives, understanding and managing cyber risk has become a matter of business survival, competitive advantage, and brand reputation. Vulnerability Assessment and Penetration Testing (VAPT), while technical in nature, must be approached with strategic foresight to ensure it delivers measurable value.
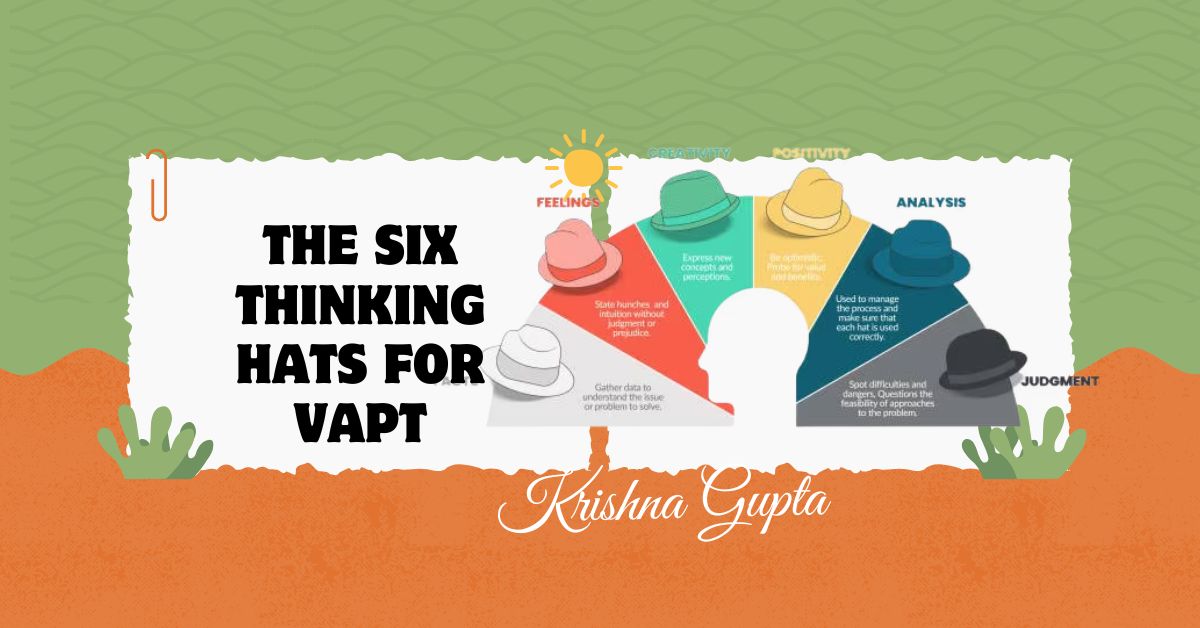
Enter Edward de Bono’s Six Thinking Hats—a powerful decision-making and innovation framework that enables multifaceted thinking. When applied to VAPT, this method provides executives with a structured way to evaluate cybersecurity investments, strategies, and risks from every critical angle. This article explores the integration of the Six Thinking Hats with VAPT planning, implementation, and optimisation.