Malware Analysis Reimagined: A C-Suite Strategy Using the Six Thinking Hats
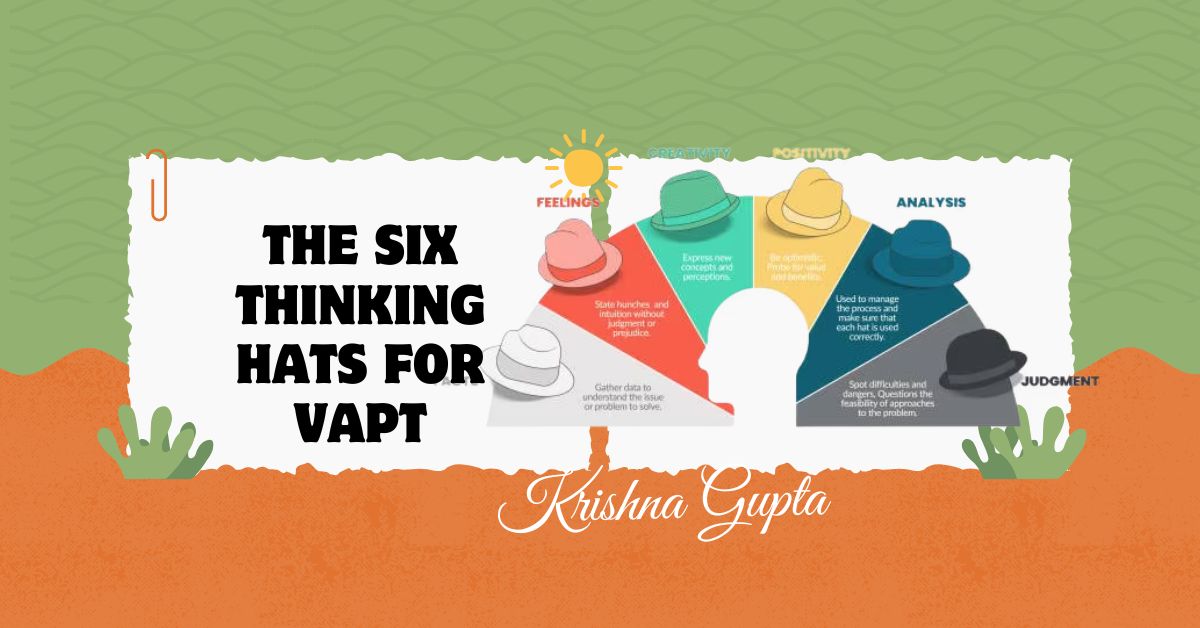
Enter Edward de Bono’s Six Thinking Hats—a parallel thinking tool used globally by Fortune 500 companies to solve complex problems. Applied to malware analysis, this method provides the C-suite with a powerful framework to examine threats from all angles—factually, creatively, emotionally, critically, optimistically, and from a control-centric view.