The OODA Loop: Your Secret Weapon for Outmaneuvering Disruption
In today’s lightning-fast business landscape, the difference between success and failure often boils down to one thing: decision speed. Disruption lurks around every corner, and CEOs who hesitate are left behind. But what if there was a framework specifically designed to accelerate your decision-making and give you a competitive edge? Enter the OODA Loop.
From Battlefield to Boardroom: The Power of the OODA Loop
Developed by military strategist John Boyd, the OODA Loop isn’t some esoteric theory. It’s a battle-tested method for outmanoeuvring opponents in dynamic environments. Imagine a chess grandmaster with several moves ahead, anticipating your every play. The OODA Loop equips you with that same foresight in the business world.
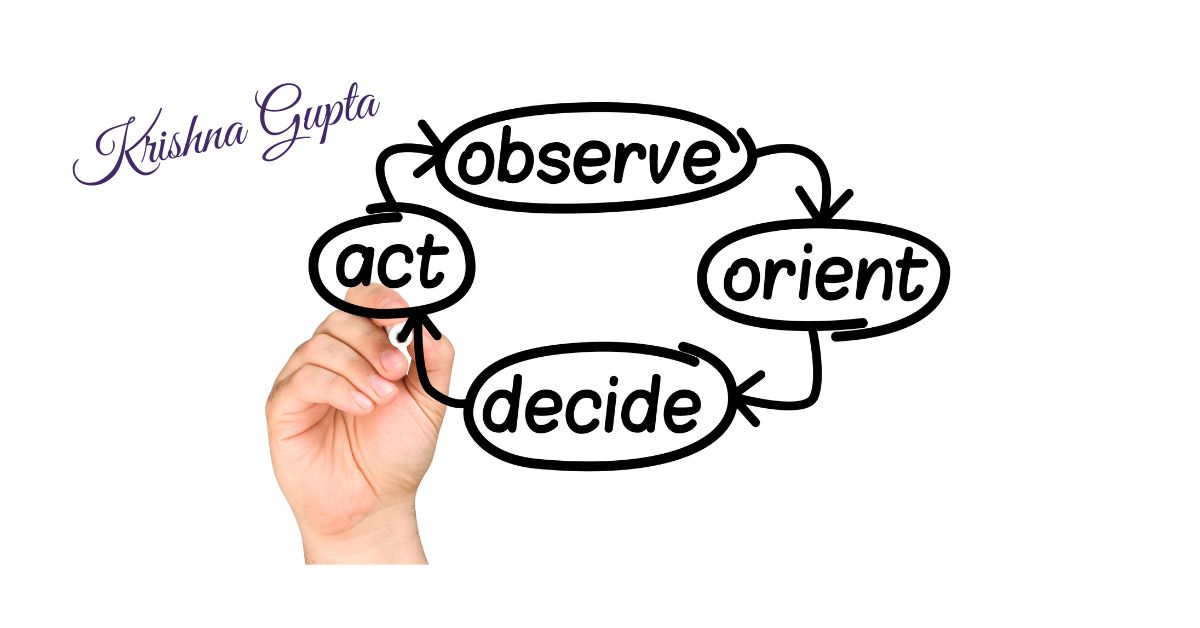
The OODA Loop: A Cyclical Advantage
Here’s how it works:
- Observe: Gather intel. This isn’t just about financial reports; it’s about scanning the horizon for emerging trends, competitor activity, and potential threats. Data analysis is crucial here, but so is fostering a culture of awareness within your organisation.
- Orient: Make sense of the data. Don’t just collect information. Contextualise it. Consider your company’s strengths and weaknesses, industry dynamics, and potential biases that might cloud your judgment.
- Decide: Chart your course. Based on your analysis, formulate a clear and actionable plan. The faster you reach a decision, the sooner you can seize opportunities or mitigate risks.
- Act: Execute with precision. Don’t get bogged down in endless planning. The OODA Loop emphasises swift and decisive action.
Here’s the beauty of the OODA Loop: it’s a continuous cycle. As you take action, you observe the results, which inform your next iteration. This lets you quickly adapt and refine your strategy, staying ahead of the curve.
The ROI of a Faster OODA Loop
Think of the OODA Loop as an investment. By compressing your decision-making cycle, you can:
- Capture fleeting market opportunities before your competitors react.
- Respond swiftly to emerging threats, mitigating potential damage.
- Boost team morale and agility, fostering a culture of innovation.
- Reduce risk by anticipating and preempting problems.
Taking Action: Implementing the OODA Loop in Your Organization
The OODA Loop isn’t a magic bullet but a powerful tool. Here are some steps to get started:
- Educate your leadership team on the OODA Loop principles.
- Invest in data analysis tools to gather and interpret critical information.
- Promote an information-sharing culture to ensure everyone has a clear picture of the business landscape.
- Conduct regular simulations to practice rapid decision-making under pressure.
The OODA Loop isn’t just about reacting and taking control. By mastering this framework, you can transform your organisation into an agile decision-making machine, ready to conquer any challenge the market throws your way. Remember, in the race for success, the fastest learner wins. So, are you prepared to take the lead?
Applications of OODA Loop
Beyond its military origins, the OODA Loop has become a versatile tool for leaders across various industries. Here’s a deeper dive into how CEOs can leverage the OODA Loop in specific areas:
1. Market Disruption and Competitive Advantage:
- Observe: Track competitor strategies, analyse customer behaviour shifts, and monitor emerging technologies that could disrupt your market.
- Orient: Assess your company’s strengths and weaknesses against these disruptions. Identify opportunities to adapt your product offerings or pivot your business model.
- Decide: Develop a proactive strategy to address the disruption. This could involve launching new products, acquiring competitors, or investing in R&D for innovative solutions.
- Act: Move swiftly to implement your chosen strategy. The faster you adapt, the less likely you are to be blindsided by disruption.
2. Crisis Management and Risk Mitigation:
- Observe: Set up early warning systems to identify potential crises such as data breaches, product recalls, or negative PR.
- Orient: Analyze the potential impact of the crisis and assess your company’s preparedness. Consider past crises and lessons learned.
- Decide: Develop a clear communication plan and mitigation strategy. This could involve damage control measures, public statements, or customer outreach plans.
- Act: Execute the plan decisively to minimise reputational damage and financial losses.
3. Negotiations and Strategic Partnerships:
- Observe: Gather intel on your negotiating partner’s goals, priorities, and potential weaknesses.
- Orient: Clearly understand your negotiation objectives and your company’s BATNA (Best Alternative To a Negotiated Agreement).
- Decide: Formulate a flexible negotiation strategy with different tactics depending on how the talks unfold.
- Act: Negotiate assertively while being open to mutually beneficial outcomes. The OODA Loop allows you to adapt your approach to secure the best deal possible quickly.
Remember, the OODA Loop is an ongoing process. As you take action and observe the results, you can fine-tune your approach and improve your decision-making agility. By integrating the OODA Loop into your organisation’s culture, you can confidently develop a significant competitive edge and navigate the ever-changing business landscape.
Disadvantages of OODA Loop
While a powerful tool, the OODA Loop has some limitations to consider. Here are some disadvantages to be aware of:
- Information Overload: The OODA Loop relies heavily on accurate and complete information during the observation phase. In today’s information age, we can be bombarded with data. Sifting through this data and identifying relevant information can be challenging. This may lead to analysis paralysis or, even worse, basing decisions on incomplete or inaccurate information.
- Oversimplification in Complex Situations: The OODA Loop is designed for fast-paced, dynamic situations. However, some business decisions require more in-depth analysis and consideration of nuances. For complex issues like mergers and acquisitions, the OODA Loop might overlook crucial factors if overused.
- Potential for Bias: The “Orient” phase involves interpreting information based on experience and existing knowledge. This can introduce unconscious bias into the decision-making process. Leaders must be aware of their biases and actively seek diverse perspectives to mitigate this risk.
- Limited Scope in Creative Fields: While the OODA Loop excels in fast-paced decision-making, it might not be ideal for fostering creativity and innovation. Activities like brainstorming or design thinking often benefit from a more open-ended approach where exploration and experimentation are critical.
Using the OODA Loop Effectively
Here are some tips to mitigate the disadvantages of the OODA Loop:
- Combine it with other frameworks: Don’t see the OODA Loop as a replacement for other decision-making tools. Use it with strategic planning frameworks for complex situations or design thinking approaches for creative endeavours.
- Focus on quality information: Invest in data analysis tools and processes to ensure you base decisions on reliable and relevant data.
- Promote diverse viewpoints: Encourage healthy debate and incorporate feedback from various stakeholders to mitigate bias in the “Orient” phase.
- Recognise its limitations: Understand that the OODA Loop is best suited for specific situations. Use alternative approaches when dealing with complex issues or fostering creative problem-solving.
By strategically acknowledging these limitations and using the OODA Loop, you can maximise its benefits and make informed and adaptable decisions in a dynamic business environment.
Applications of OODA Loop in Information Security
The OODA Loop: Your Secret Weapon for Outmaneuvering Cyberattacks
Cybersecurity is a constant battle; staying ahead of attackers requires a proactive approach. The OODA Loop, a decision-making framework originally developed for military strategy, can be a powerful tool for information security teams. It empowers them to outmanoeuvre attackers by making faster and more informed decisions.
Why the OODA Loop Works for Cybersecurity
Traditional security strategies often focus on reaction. You wait for an attack, then scramble to contain the damage. The OODA Loop flips this script, promoting a proactive and adaptable approach:
- Observe: Security teams continuously monitor networks, systems, and external threat intelligence feeds. This includes security logs, vulnerability reports, attacker tactics, techniques, and procedures (TTPs).
- Orient: Security analysts interpret the collected data to understand the current threat landscape. They identify potential vulnerabilities in your systems and consider the attacker’s motivations and capabilities.
- Decide: Based on the observed threats and your organisation’s risk tolerance, security leaders make informed decisions about security controls, incident response plans, and resource allocation.
- Act: Security teams implement the chosen security measures, such as patching vulnerabilities, deploying intrusion detection systems (IDS), or conducting security awareness training.
The OODA Loop in Action: Countering Phishing Attacks
Let’s see how the OODA Loop applies to a specific cybersecurity scenario:
- Observe: Security analysts identify a rise in phishing emails targeting your company.
- Orient: The team analyses the emails, recognising a new tactic attackers use to bypass existing email filters.
- Decide: Security leaders launch a targeted employee awareness campaign to educate employees on identifying these new phishing attempts.
- Act: The security team creates training materials and conducts phishing simulations to test employee awareness and strengthen your organisation’s first line of defence.
Benefits of the OODA Loop for Information Security
By adopting the OODA Loop, your security team can:
- Reduce dwell time: Faster detection and response minimise the window of opportunity for adversaries to exploit vulnerabilities and steal data.
- Proactive threat hunting: Move beyond just reacting to threats and actively hunt for potential vulnerabilities and attacker activity within your network.
- Improved decision-making: OODA Loop fosters a culture of information sharing and analysis, leading to more informed security decisions.
- Enhanced situational awareness: Security teams gain a clearer picture of the evolving threat landscape and can adapt their defences accordingly.
Implementing the OODA Loop in Your Security Strategy
Here are some steps to integrate the OODA Loop:
- Security Information and Event Management (SIEM) systems to centralise log collection and analysis.
- Train your security team on threat intelligence gathering and analysis techniques.
- Conduct regular security drills to practice rapid decision-making under pressure.
- Promote a culture of information sharing between security teams and other departments.
The OODA Loop isn’t a one-time fix; it’s a continuous cycle. By constantly observing, orienting, deciding, and acting, your security team can develop a proactive and adaptable security posture, staying ahead of cyber threats and protecting your valuable data.
Disadvantages of OODA Loop in Information Security
The OODA Loop shines in information security, but it’s not without limitations in this specific context. Here are some disadvantages to consider:
- Complexity of Cyber Threats: While the OODA Loop emphasises speed, cyberattacks can be highly sophisticated and constantly evolving. Attackers may employ social engineering tactics or zero-day exploits that require more nuanced analysis beyond the rapid decision-making cycle of the OODA Loop.
- Resource Constraints: Security teams are often understaffed and overworked. The OODA Loop requires continuous monitoring, analysis, and decision-making, which can strain already stretched resources. Smaller teams might struggle to implement all stages effectively.
- Imperfect Information Security Tools: Security tools like SIEM systems and intrusion detection/prevention systems (IDS/IPS) generate a lot of alerts. However, these alerts can be noisy and have a high rate of false positives. Relying solely on automated tools for observation can lead to missed threats or wasted time investigating false alarms within the OODA Loop.
- Human Error: The OODA Loop is only as effective as those using it. Security analysts can make mistakes during observation, orientation, or decision-making. Fatigue or cognitive biases can cloud judgment and lead to suboptimal security decisions.

Addressing the OODA Loop’s Disadvantages in Security
Here’s how to mitigate these limitations and leverage the OODA Loop for more robust information security:
- Combine with Threat Intelligence: Integrate threat intelligence feeds into the OODA Loop to gain a broader understanding of attacker motivations, capabilities, and TTPs (Tactics, Techniques, and Procedures). This can help security teams anticipate and prioritise threats during the observation and orientation.
- Prioritise and Automate: Security tools can be valuable for observation, but prioritise high-fidelity alerts and focus analyst time on investigating the most critical threats—Automate routine tasks to free up security personnel for complex analysis and decision-making within the OODA Loop.
- Invest in Training and Automation: Continuously train your security team to improve their observation, analysis, and decision-making skills. Invest in tools that automate repetitive tasks and leverage machine learning to reduce false positives from security alerts.
- Promote a Culture of Security Awareness: Educate all employees on cybersecurity best practices to strengthen your first line of defence. This can help reduce the number of successful social engineering attacks and improve overall security stance.
By acknowledging these limitations and taking steps to mitigate them, you can leverage the OODA Loop’s strengths to create a more responsive and adaptable information security strategy. Remember, the OODA Loop is a tool, and its effectiveness depends on how it’s used within your organisation’s specific security framework.